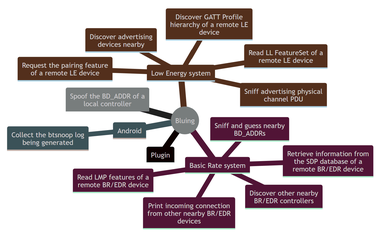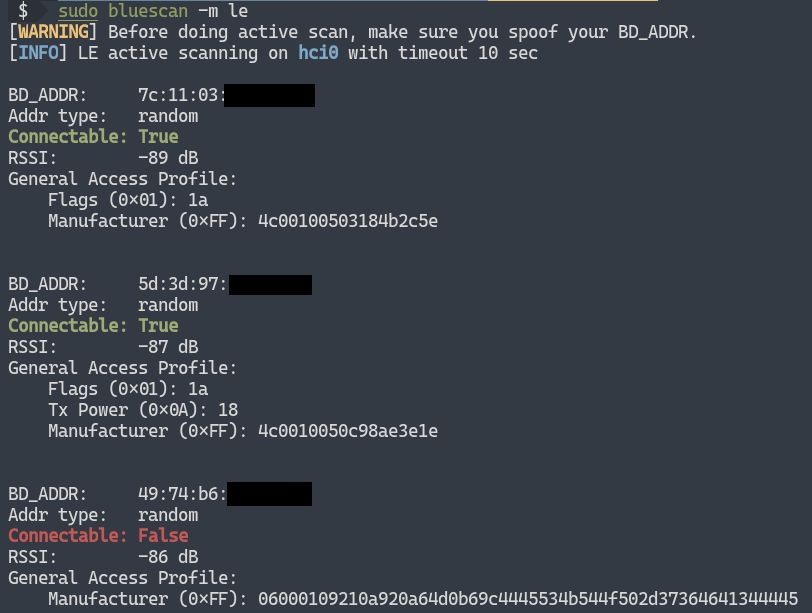
Bluescan - A Powerful Bluetooth Scanner For Scanning BR/LE Devices, LMP, SDP, GATT And Vulnerabilities!
BLURtooth Attack - A Bluetooth Vulnerability To Overwrite Authentication Key - Hackers Online Club (HOC)
Scan your Dart and Flutter dependencies for vulnerabilities with osv-scanner | by Yong Shean | Medium
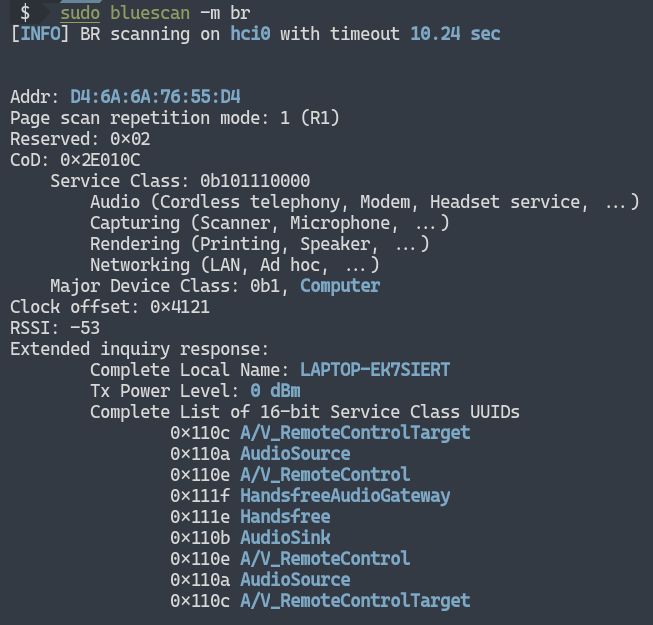
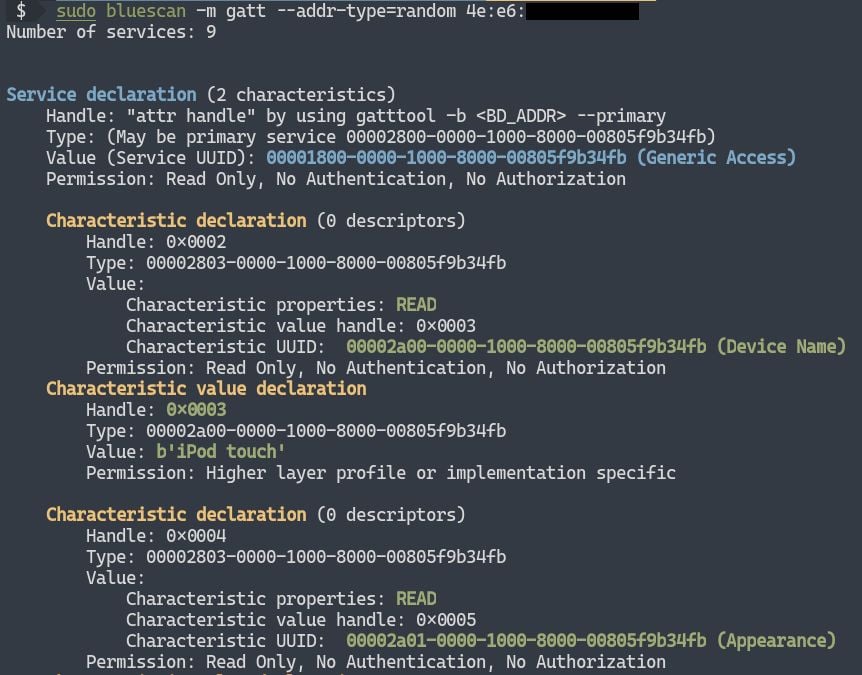
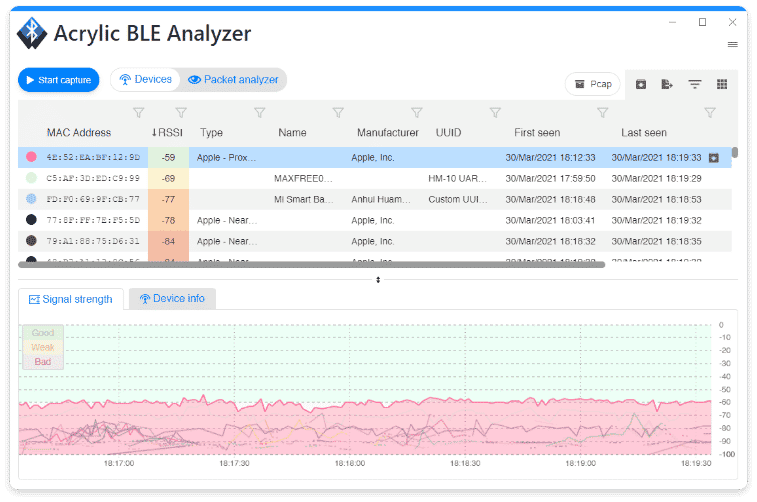
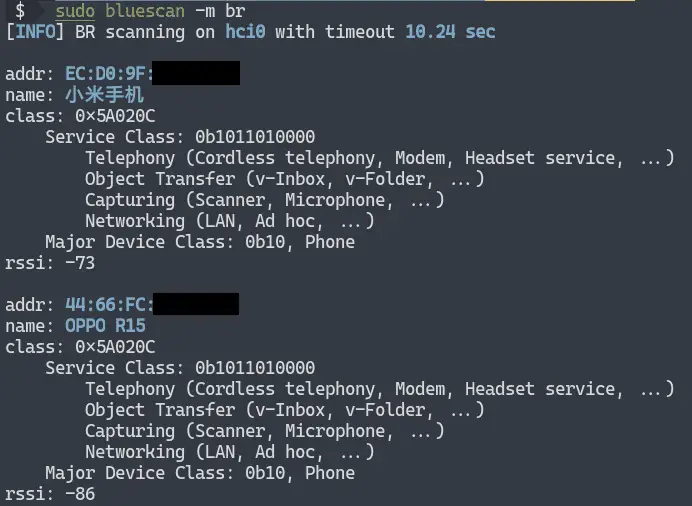
Bluescan - A Powerful Bluetooth Scanner For Scanning BR/LE Devices, LMP, SDP, GATT And Vulnerabilities!

Bluetooth vulnerability can be exploited in Key Negotiation of Bluetooth (KNOB) attacks | Malwarebytes Labs

BleedingTooth: Google drops full details of zero-click Linux Bluetooth bug chain leading to RCE | The Daily Swig
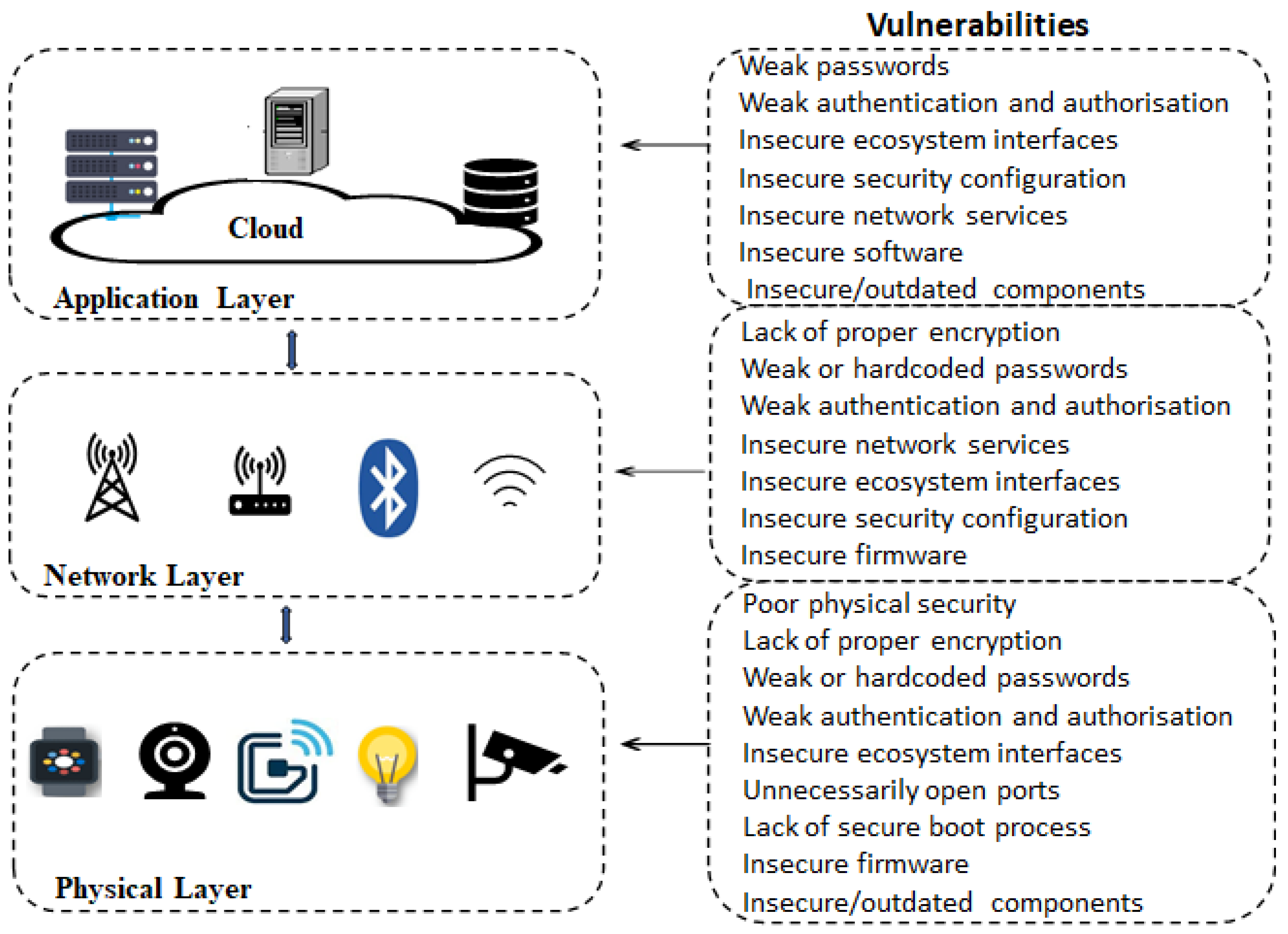
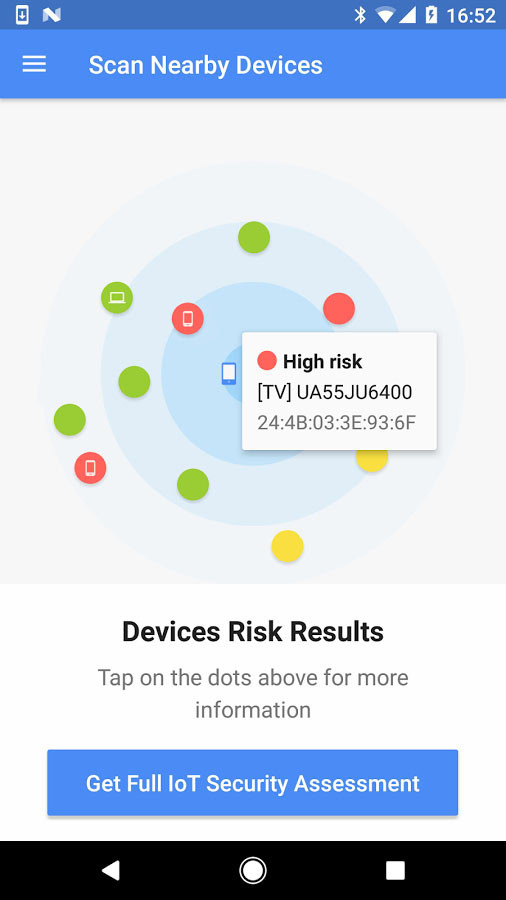
Electronics | Free Full-Text | Analysis of Consumer IoT Device Vulnerability Quantification Frameworks
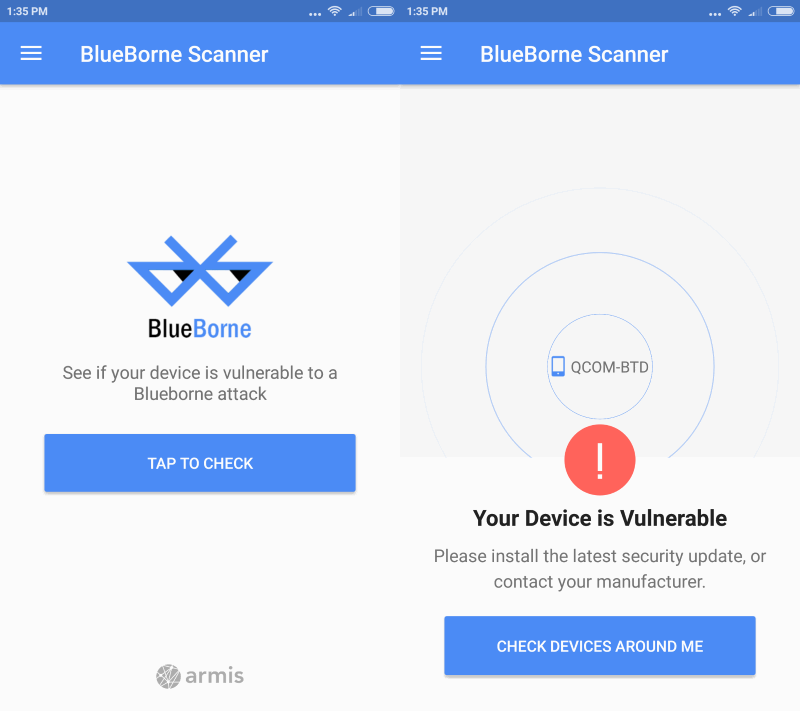
![Download] Use the official BlueBorne Vulnerability Scanner app to check if your phone is safe - TalkAndroid.com Download] Use the official BlueBorne Vulnerability Scanner app to check if your phone is safe - TalkAndroid.com](https://i0.wp.com/img.talkandroid.com/uploads/2017/09/BlueBorne-e1505385848852-900x533.png?resize=900%2C533&ssl=1)